Responsible State Behaviour in Cyberspace: Where are we headed?
I recently read a report of an Open-Ended Working Group (OEWG) mandated by the United Nations (UN) to advance work on developing standards of responsible state behaviour in cyberspace. On digging a little deep into the work of this group, I had a lot of open-ended questions in my mind in context to the recent technological developments in cyberspace and the ongoing battle of tech norms. So let me build some context for you.
United Nations (UN) has been home to debates and negotiations on the rules, norms, and principles of states’ responsible behaviour in cyberspace since I was born (the early 1990s). So what is responsible state behaviour in Cyberspace?
Responsible behavior in cyberspace refers to the actions and activities of states and other actors in the digital domain that are consistent with international laws, norms, and principles. These behaviors are aimed at promoting the stability, security, and prosperity of cyberspace, while also respecting the sovereignty and rights of other states and individuals.
I am aware that one of the earliest efforts to address this issue was the UN Group of Governmental Experts (GGE) on Developments in the Field of Information and Telecommunications in the Context of International Security, which was established in 1998. This group has held a series of meetings and produced several reports on issues related to international security in cyberspace. In the last three years, I have noticed a lot of chatter and attention in the Global Internet Community about the two international working groups mandated by the UN on this issue. The two groups are:
- The Open-Ended Working Group on Developments in the Field of ICTs in the Context of International Security (OEWG 2021), established by the UN General Assembly in December 2018 (UN General Assembly Resolution A/RES/73/27 2018)
- 6th UN Group of Governmental Experts (GGE) on advancing responsible state behaviour in cyberspace in the context of international security (UN Group of Governmental Experts 2021), also established in December 2018 (UN Resolution A/RES/73/266 2018)
The first group OEWG was mandated:
to further develop the rules, norms, and principles of responsible behavior of States…, and the ways for their implementation; if necessary, to introduce changes to them or elaborate additional rules of behavior; to study the possibility of establishing a regular institutional dialogue with broad participation under the auspices of the United Nations; and to continue to study…existing and potential threats in the sphere of information security and possible cooperative measures to address them and how international law applies to the use of information and communications technologies by States, as well as confidence-building measures and capacity-building.
This group submitted its report in March 2021. Recognising the COVID-19 pandemic, the OEWG group was renewed for 2021–2025. The GGE was tasked:
to continue to study, with a view to promoting common understandings and effective implementation, possible cooperative measures to address existing and potential threats in the sphere of information security, including norms, rules and principles of responsible behavior of States, confidence-building measures and capacity-building, as well as how international law applies to the use of information and communications technologies by States.
The GGE submitted its report in May 2021.
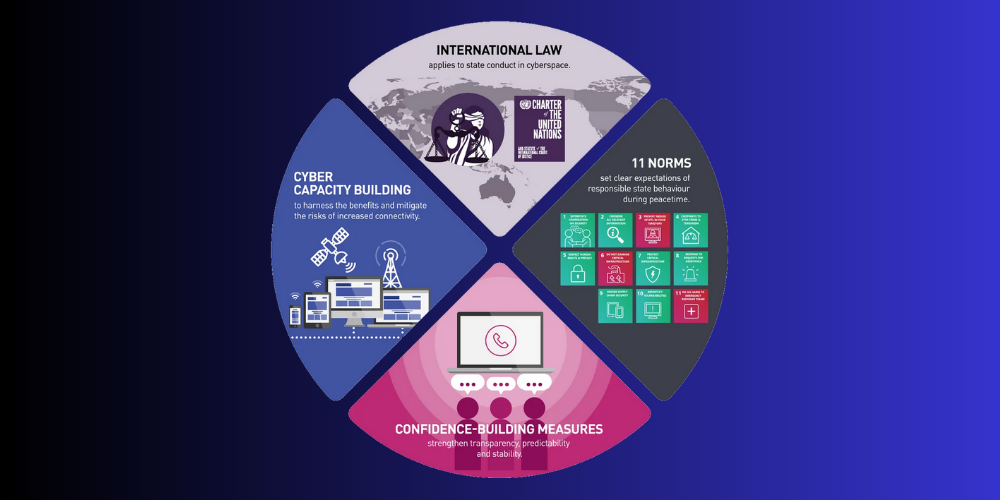
In light of ever-deteriorating geopolitical tension, it is important to acknowledge the success of both groups to arrive at a consensus text (which means Member States agree to adopt the draft resolution without taking a vote). Both the OEWG and GGE 2021 managed to get their participating 193 and 25 states to align their positions at least to what currently constitutes the minimal common denominator. To promote stability, the members of the United Nations have developed a framework that clearly articulates what states should and should not do in cyberspace. This framework for responsible state behaviour has four pillars. The first is that international law, including the Charter of the United Nations, applies to state conduct in cyberspace. Next are 11 agreed norms that set clear expectations of responsible state behaviour during peacetime. Those norms are supported by confidence-building measures which strengthen transparency, predictability, and stability. The last pillar is cyber capacity building to ensure all states can harness the benefits and mitigate the risks of increased connectivity.
This does not mean that disagreements among states have been resolved, rather I would say that they had their will and opportunity to keep them on one side and reconfirm the positions of other states.
As there is already a lot of information available about the work of these groups on the internet, I will not go into detail on the reports of these groups. I will briefly cover some important achievements of both groups and then the normative impacts that they have produced over time, specifically in the technical community, as well as the questions they leave open now.
Industry sometimes underestimates the UN’s work in this field because it is slow, not far-reaching in practical terms, and detached from real-world challenges. Its recommendations so far are legally non-binding and do not seem to restrain malicious cyber activity in a tangible way. I recognise that the work of these groups on the internet has significant “spill-over” effects, meaning it has the ability to fundamentally change how we approach and address cyber threats at a global level. Even though there is still discussion about how to turn these recommendations into concrete commitments and actions by states, since they come from “soft law”, I recognize that small but meaningful changes could lead to a more comprehensive understanding and response to the rapid increase in cyber threats and their impact on the global community. The 6th GGE has made a serious effort to provide guidance on this issue.
I believe that these shifts are building bridges ‘with the real world, at the same time leaving some questions still unanswered. They are an important reflection of what these past few years have meant to the cybersecurity field in general and what might lie ahead. I find such an exercise to be useful in the short-term, as the OEWG 2021–2025 starts its work, for the broader work on cyber peace and security under the auspices of the UN, and even more so for all the states and other stakeholder groups that are willing to carry this work further.
The evolution of Tech Norms
The United Nations (UN) has played a significant role in shaping tech norms in the cyber domain, which has had an impact on other stakeholders including governments, academia, civil society, and the private sector. This has led to agenda rivalry among state and non-state platforms, but it has also pushed all involved stakeholders to advance their thinking and action. The UN’s tech norms are shaped by values and principles that differ from those of the internet’s sociotechnical imaginaries, which are based on principles of end-to-end connection, openness, and permissionless innovation. These shifts in values have been reflected in technical self-governance over time and are influenced by the UN processes and related expectations. Examples of technical community initiatives that have sought to develop normative regimes include Mutually Agreed Norms for Routing Security (MANRS), the Internet Governance Forum’s (IGF) Best Practice Forum on Internet Security, the Internet Engineering Task Force (IETF), and the Internet Architecture Board (IAB). These initiatives demonstrate ongoing efforts to address cyber threats and promote stability in the cyber domain.
The EU’s DNS4EU initiative aims to develop a public European DNS resolver service that follows security, data protection, and privacy standards. There are concerns about DNS4EU potentially being used for state control of information flows. The emergence of DNS encryption protocols, such as DNS over TLS and DNS over HTTPS, may also affect the resolver operator market and raise consumer expectations. These protocols also raise privacy concerns, as encrypted messages become indistinguishable from other HTTPS non-DNS traffic, potentially allowing a small group of widely used public resolvers to dominate the market. The EU’s DNS4EU initiative highlights the conflict between different norms and values. On the one hand, user privacy is valued in the IETF environment where DNS encryption protocols such as DNS over TLS and DNS over HTTPS were developed, and is also an important value in Europe. At the same time, the adoption of these protocols challenges the EU’s concept of digital sovereignty or strategic autonomy. This norm, promoted by the European Commission, is also reflected in EU digital diplomacy in the UN processes. The concept of sovereignty has gained more support in the EU, possibly due to the EU’s reevaluation of its role in the global community and its desire for strategic autonomy. This value will be pursued through legislative and infrastructure initiatives but may conflict with the values of an open internet or privacy. It will be interesting to see how this norm is translated into EU foreign digital policy and diplomatic efforts at the UN and how it is reconciled with other socio-technological norms.
The United Nations (UN) Open-Ended Working Group (OEWG) and the UN Group of Governmental Experts (GGE) have both discussed the evolving threat context for international peace and security in relation to the use of information and communication technologies (ICTs). This includes the development of new military cyber capabilities by an increasing number of countries, as well as the impact of emerging technologies on the attack surface and vulnerabilities that can be exploited for malicious ICT activity. One such emerging technology is artificial intelligence (AI), which has a multi-dimensional relationship with cybersecurity and can be used as both a tool for cyber defense and a means of carrying out cyber-attacks. The adoption of AI as a technology is outpacing regulatory and norms-building efforts, resulting in technical, political, and ethical governance challenges. The use of AI in cyber capabilities also has the potential to create a new arms race, as leading world powers seek to gain a competitive advantage in the development of AI-driven cyber defense and offense capabilities. There are also concerns about the impact of AI on employment and the potential for further economic inequality. The UN processes may not be able to effectively address these emerging threats, leading to significant gaps in risk assessment for global peace and security.
The conflict between Tech Norms and UN Norms in Cyberspace
I understand that it is possible (and its happening) for tech norms to conflict with UN norms for cyberspace, as these norms may have different goals or priorities. For example, some tech norms may prioritize the protection of personal privacy, while UN norms for cyberspace may prioritize the stability and security of the digital domain. One example of a tech norm that may conflict with UN norms for cyberspace is the use of encryption. Tech norms related to privacy may encourage industry to use encryption to protect their PPI data and information from unauthorized access. However, UN norms for cyberspace may prioritize the ability of states to access and monitor the digital communications of their citizens in order to protect national security. In this case, the tech norm of protecting personal privacy may be in conflict with the UN norm of protecting national security. Another example of a tech norm that may conflict with UN norms for cyberspace is the use of artificial intelligence (AI). Tech norms related to ethical use may encourage industry to develop and use AI in a responsible manner, while UN norms for cyberspace may prioritize the use of AI for military or other strategic purposes. In this case, the tech norm of ethical use may be in conflict with the UN norm of using AI for national security purposes.
The conflict between tech norms and UN norms on responsible state behaviour in cyberspace that has been exacerbated by the ongoing conflict in Ukraine. The conflict in Ukraine has involved a number of cyber-attacks and other forms of cyber warfare, which have raised concerns about the responsible use of technology and the role that states should play in regulating cyber activity. This includes the use of cyber attacks to disrupt critical infrastructure and the use of cyber espionage and propaganda to interfere in the domestic politics of other countries. These activities violate international norms of state behaviour and have led to calls for greater regulation and accountability in cyberspace. The conflict in Ukraine has therefore highlighted the need for greater international cooperation and the development of clear norms and rules of behaviour in cyberspace.
Conclusion
I have not tried to analyse all the consequences of the work done by the OEWG and the GGE in this article. However, it is important to note that there have been several major changes in the way that responsible state behaviour in the use of ICTs is perceived, especially the relationship between political and technical norms. These changes have been influenced by the increased recognition of the importance of the stability and resilience of the internet and ICTs for human well-being. While the UN processes on this issue are slow and limited, they have helped to develop a field of thought and have indirectly contributed to the development of accountability practices in the tech community in response to cybersecurity challenges through the broader discourse on norms-building. It will be interesting to see how the relationship between tech responsibility and tech regulation, particularly in the DNS world, will evolve. For example, the transparency reporting format, which started as a Google project in 2009 and was adopted by other internet companies in 2013 in response to the surveillance revelations by Edward Snowden, has now become a standard industry accountability format. In 2020, the EU Digital Service Act required all online intermediaries offering services in the EU single market, whether based in the EU or not, to publish a transparency report. While the norms-building discussions have had some impact, there are also areas where they have limitations, such as the disconnect between the norms on the agenda and the cyber activities that are incompatible with these norms and not properly addressed by current international law in cyberspace. Additionally, some existing and rapidly evolving cyber capabilities may already challenge the meaningfulness of current agreements.
In my understanding it may be useful for the UN to consider ways to bring together state actors and non-state actors to discuss the current gap between UN norms and tech norms. By taking an inclusive approach and involving a diverse range of stakeholders in this process, it may be possible to establish norms that can be formally adopted as binding resolutions for both states and non-state actors. Though, the binding resolutions are far fetching. This could help to bridge the divide between these two spheres and promote greater coherence and alignment in the way that technology is governed and used. We are already at a historic juncture due to the Ukraine war destroying western unity as the US is profiting from the war and the EU is not liking it. It will be interesting to see how the UN, states, private stakeholders and Cyber Security Community will respond to the situation which have led to calls for greater regulation and accountability in cyberspace.
Attribution & Resources:
- Developments in the field of information and telecommunications in the context of international security — UNODA
- Open-ended working group on information and communication technologies (2021) | United Nations
- The UN Struggles to Make Progress on Securing Cyberspace — Carnegie Endowment for International Peace
- Major tech groups, nonprofits iced out of UN working group on cybersecurity norms | SC Media
- Tech-Accord-OEWG-response-March-2021
- The UN norms of responsible state behaviour in cyberspace — Australia
- 2021 OEWG report
- Cyber norms: technical extensions and technological challenges